Utilize Kms for File Upload to S3
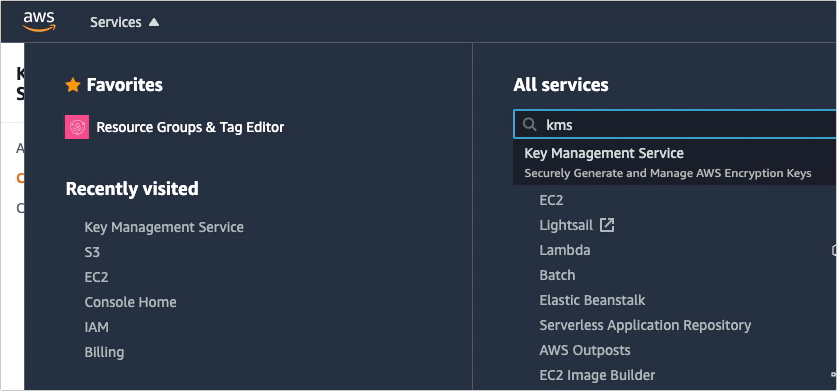
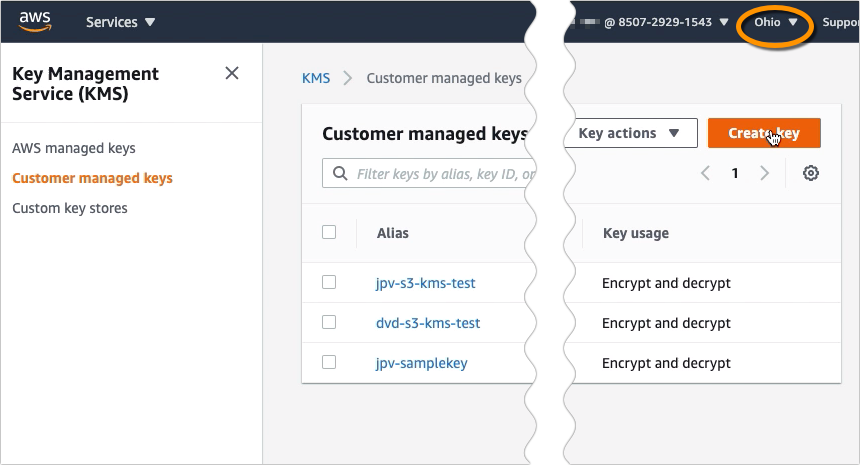
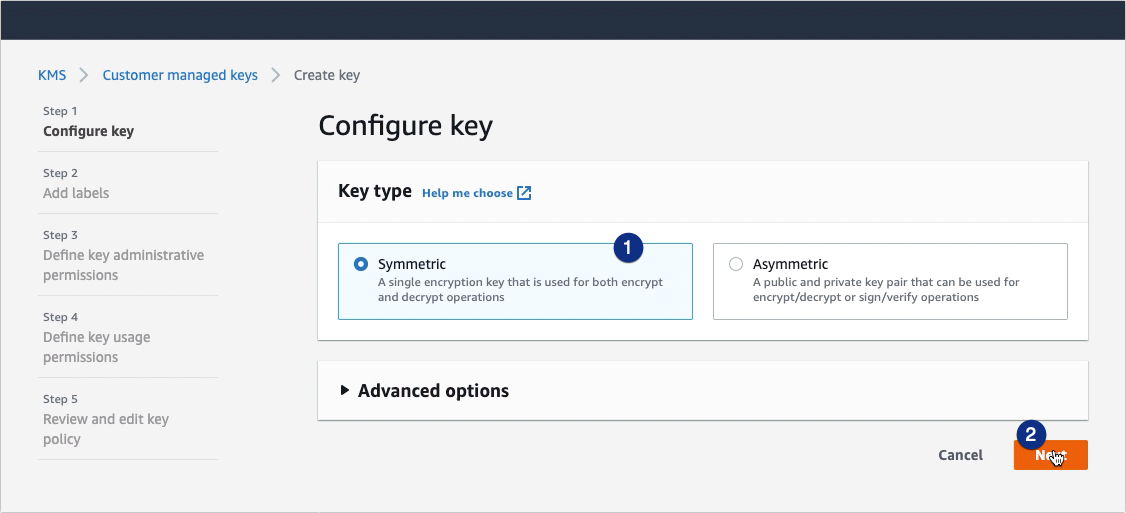
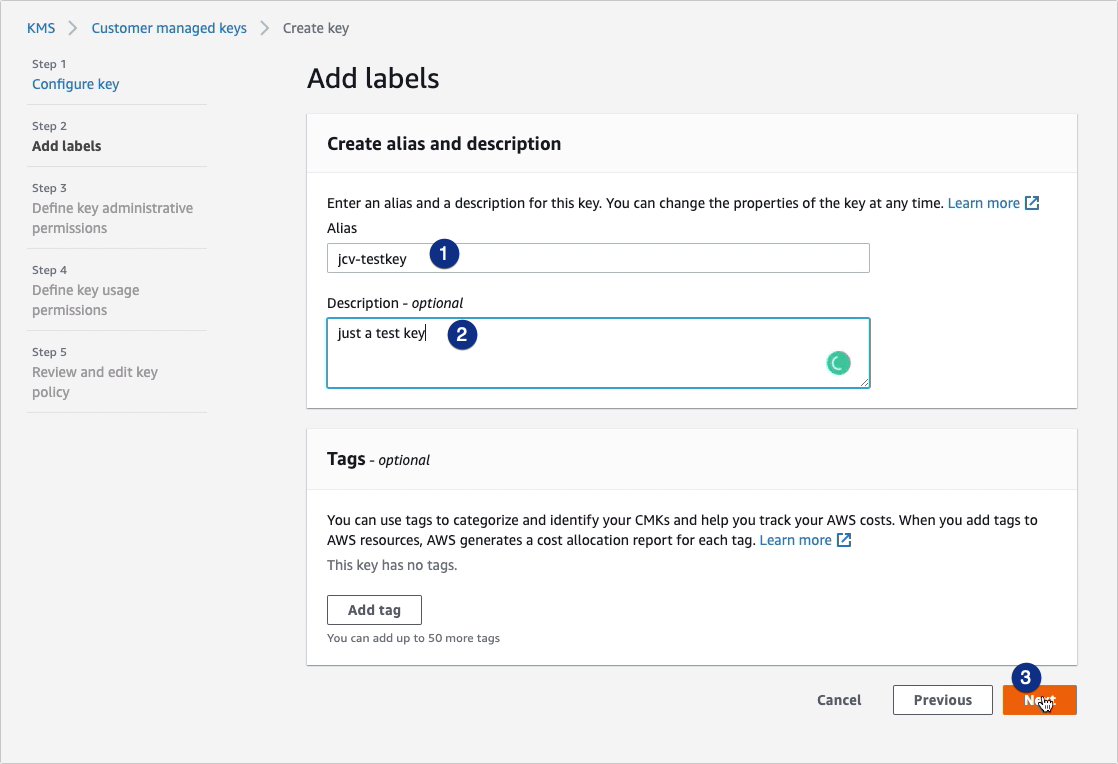
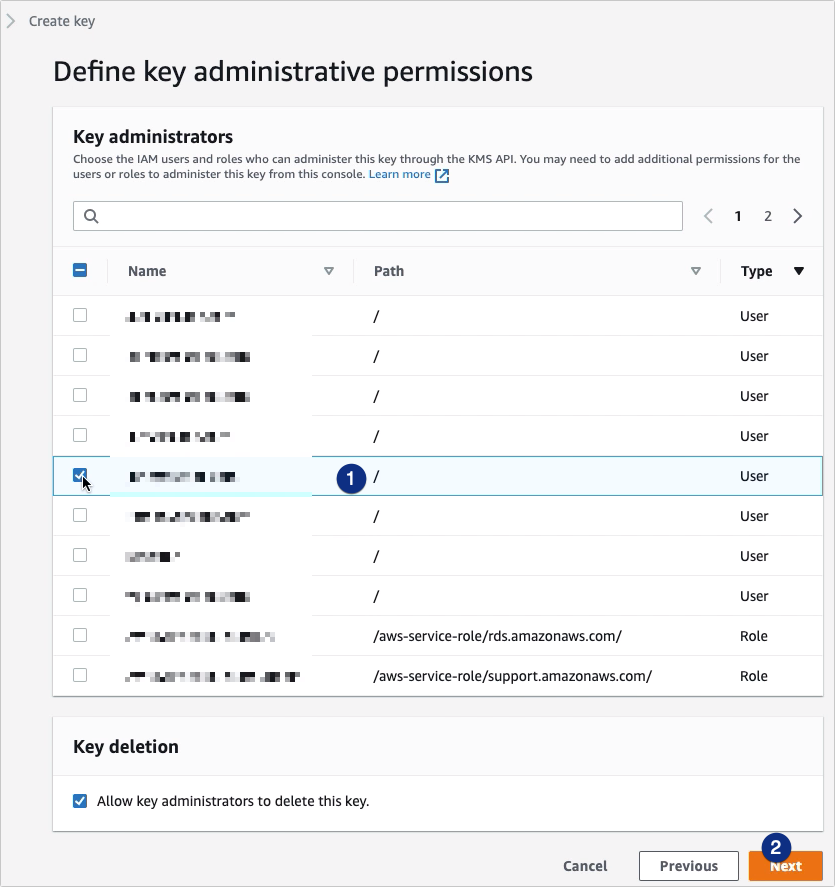
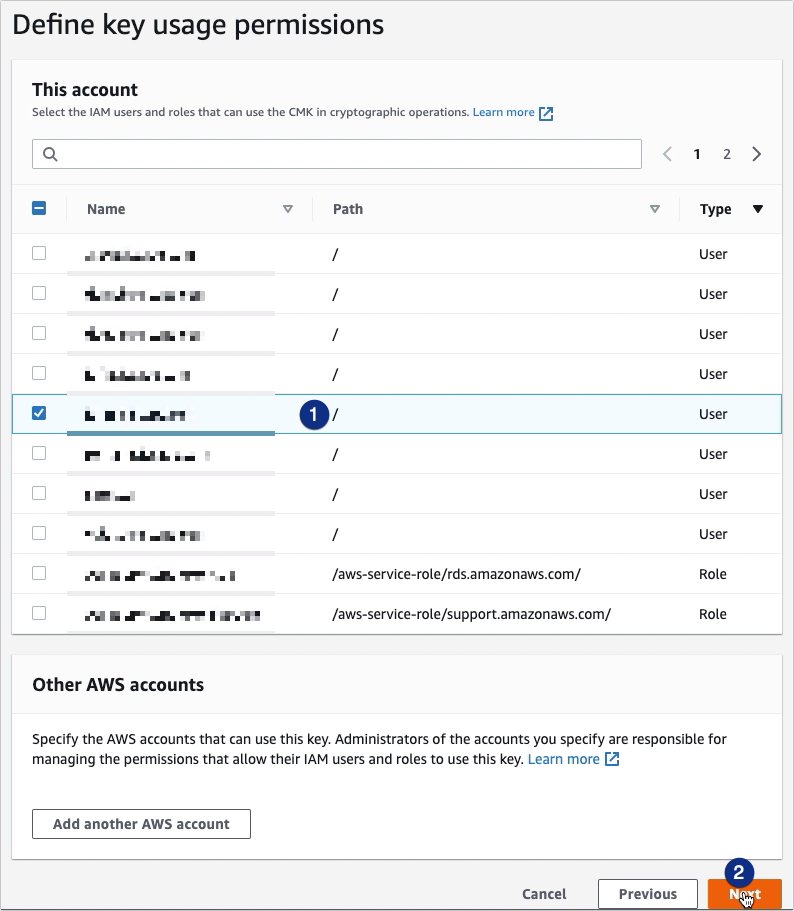
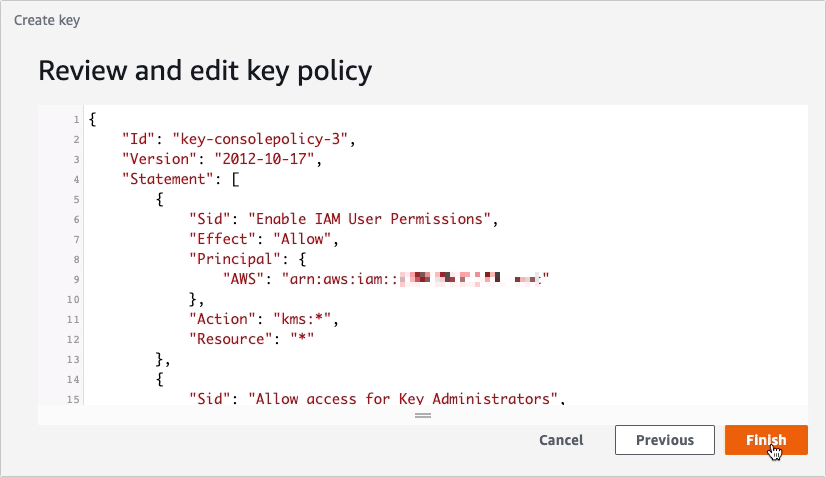
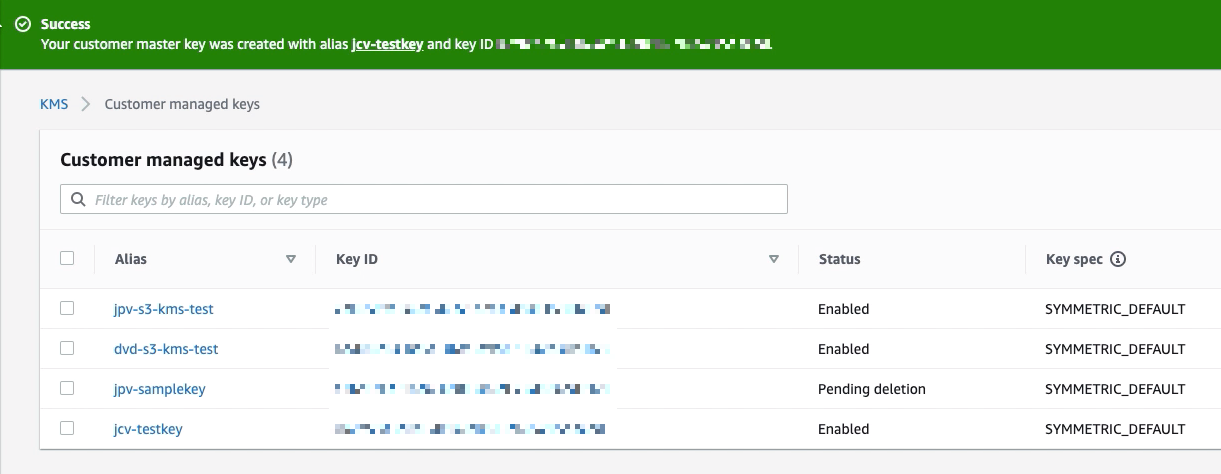
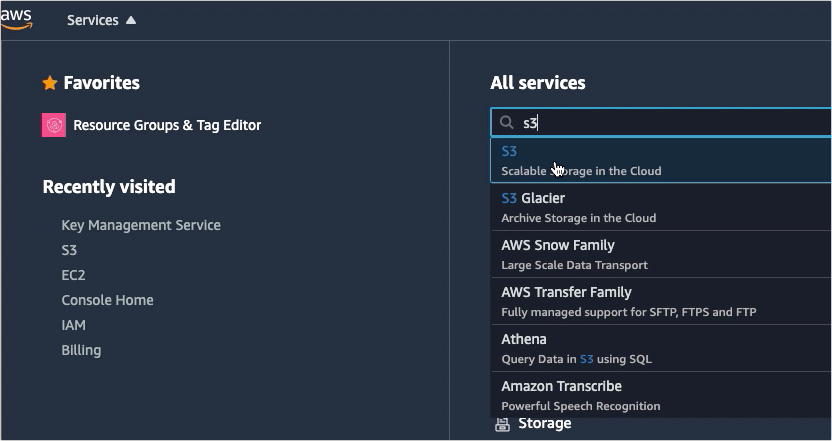
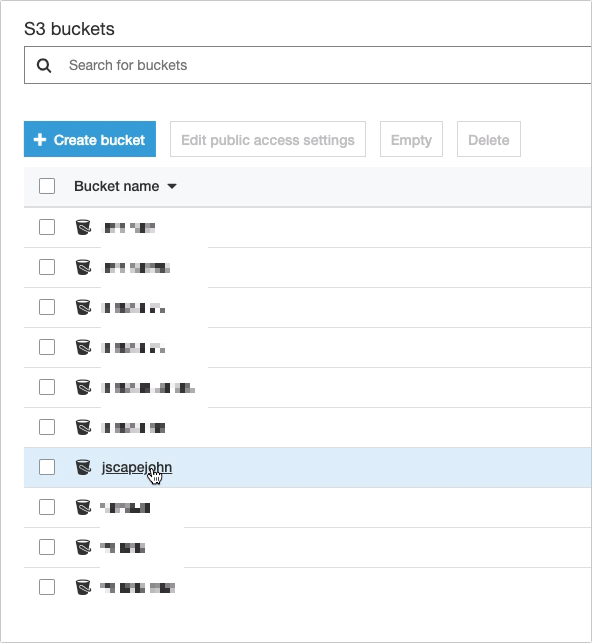
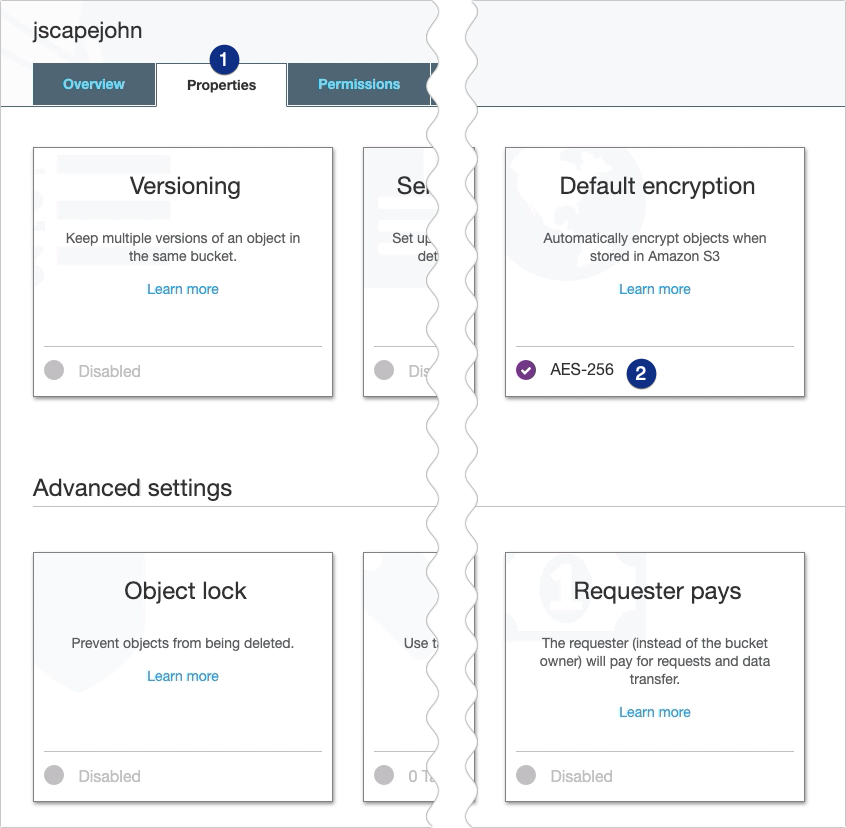
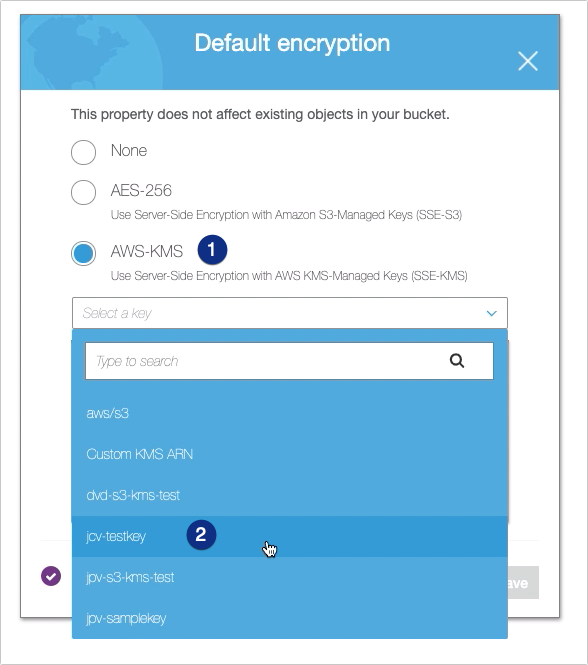
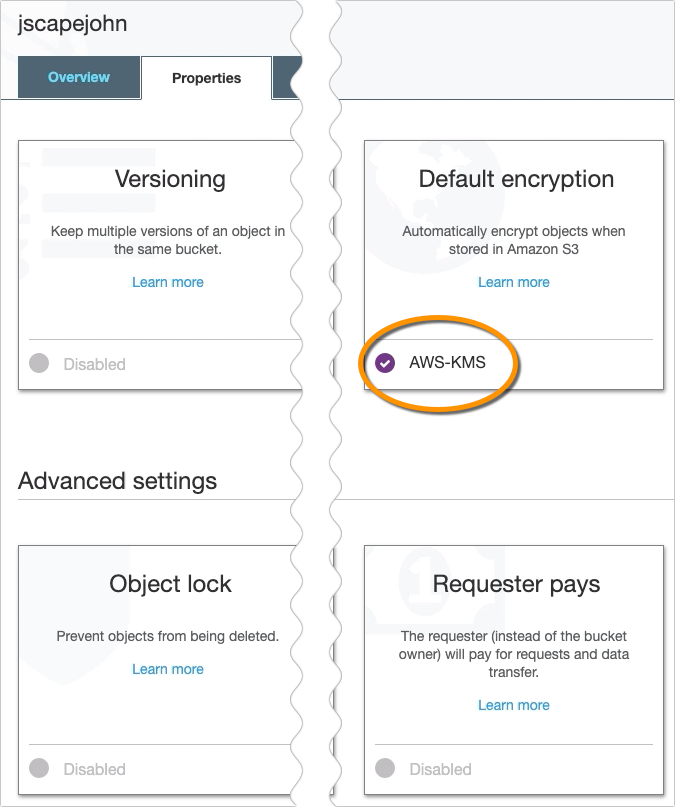
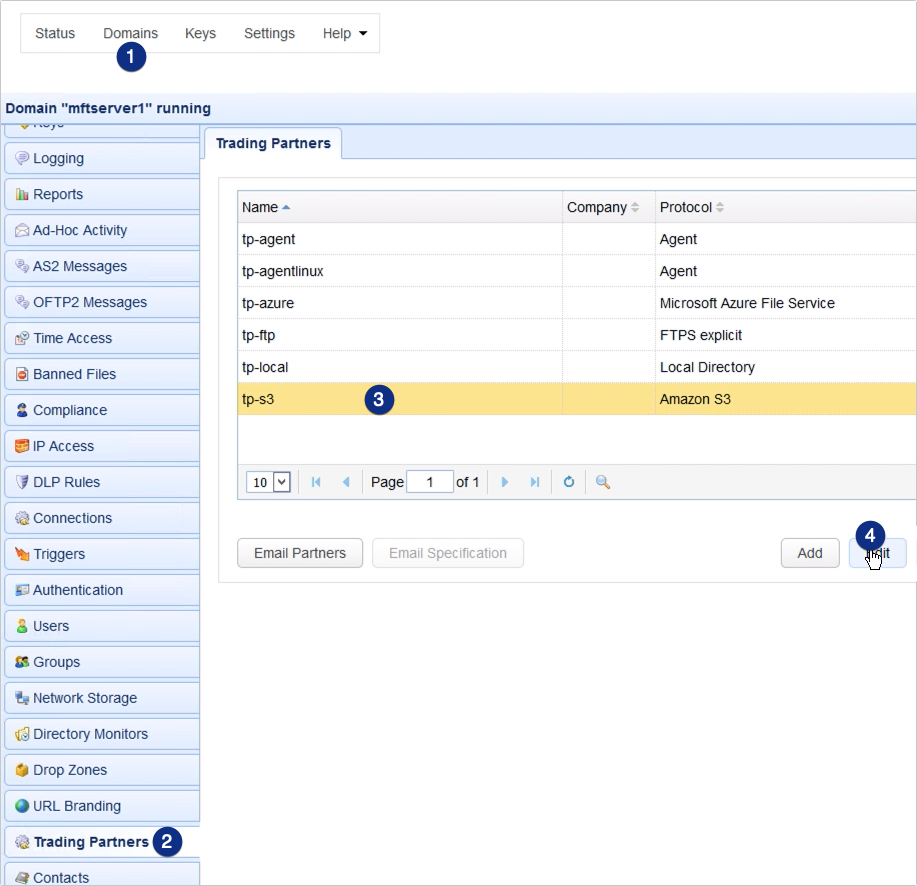
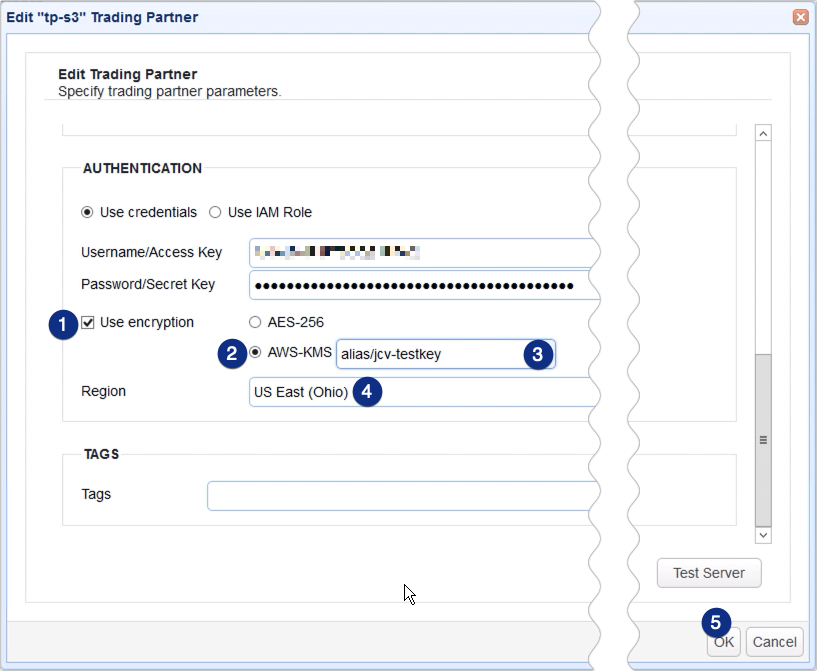
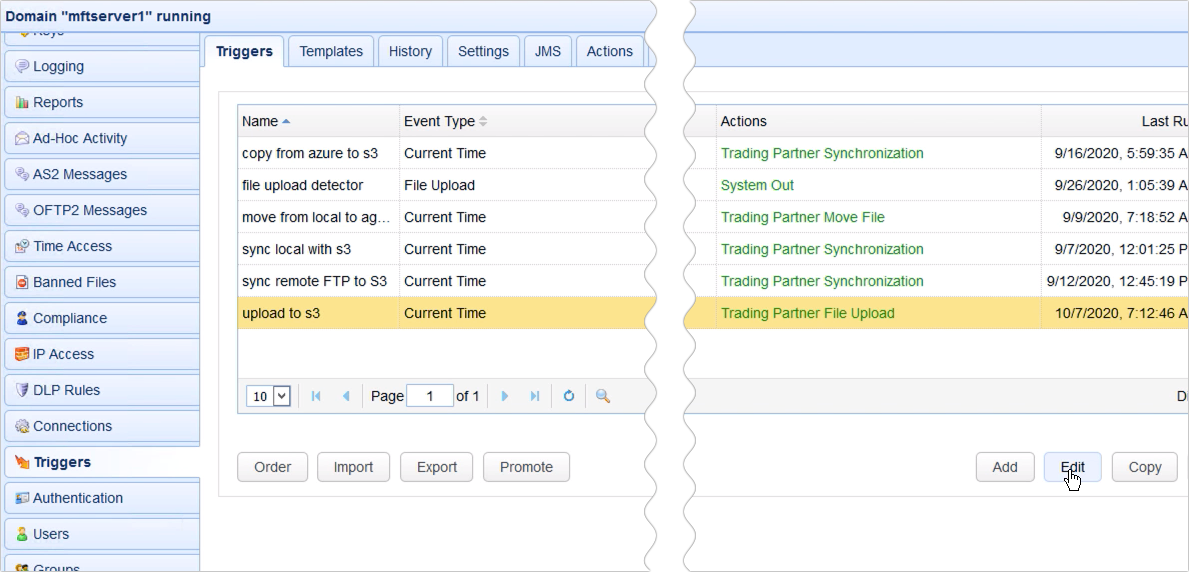
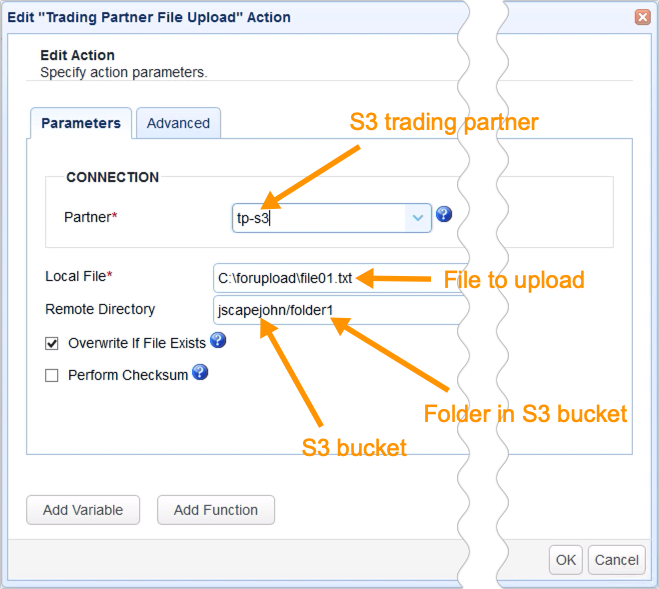
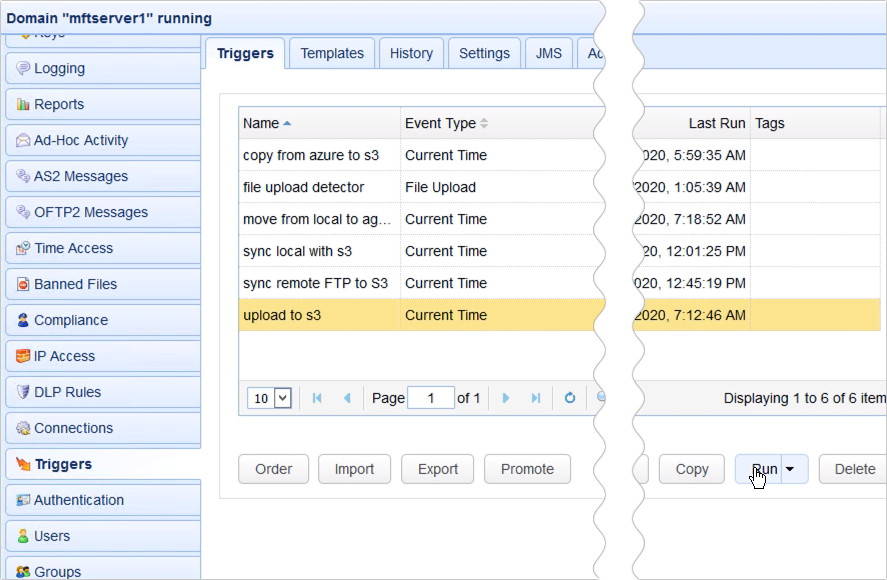
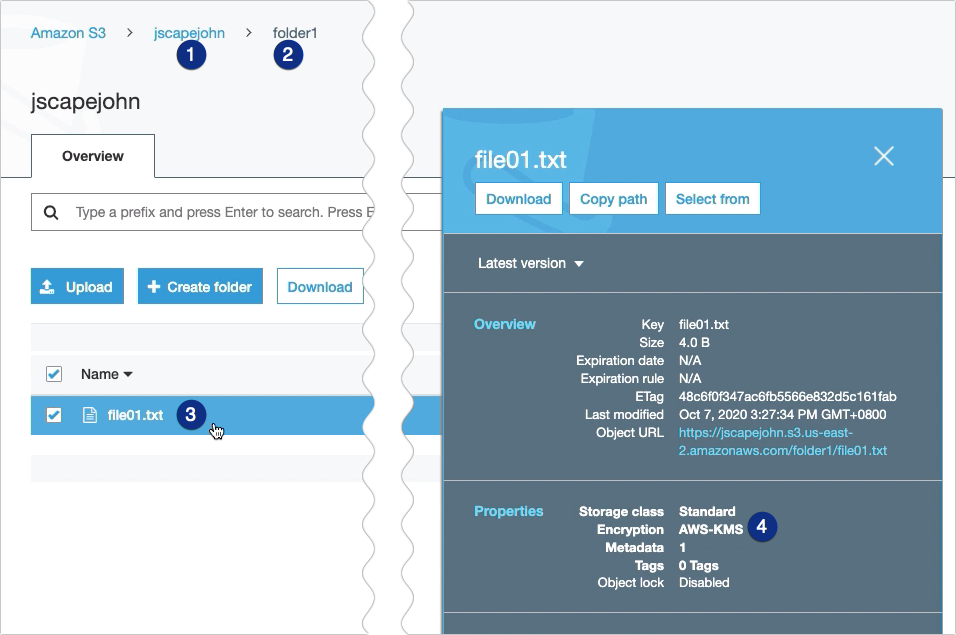
Files you upload to an Amazon S3 trading partner through JSCAPE MFT Server are normally stored in plaintext. If you want to encrypt those files to minimize the hazard of a data breach, one mode to exercise that is by using the AWS Cardinal Management Service or AWS KMS. We'll show yous how to utilize this particular service in this postal service. Would you prefer to sentinel a video version of this tutorial instead? You can play the video below. Otherwise, merely skip it if you wish to keep reading. Note that at that place are costs associated with the AWS KMS service, and then I suggest y'all read this page on the AWS website first. Alright. The first thing you need to practice is to create a client chief key or CMK. You can create this key through either the AWS KMS API or the AWS Management Console. Nosotros'll be using the latter. Login to your AWS Management Console and go to the Key Management Service. If you haven't used that service notwithstanding, the easiest way to find information technology is by merely typing it into the search box as shown in the screenshot below. Pay attention to the region displayed at the upper-right corner of the screen. While yous may change that region, just brand sure it'southward the aforementioned region yous select in your JSCAPE MFT Server Amazon S3 trading partner object. Click the Create central push button to offset creating your CMK. We'll just be creating a very basic CMK, and so if you want to know more than almost all the relevant concepts and advanced settings, I suggest you lot read the AWS KMS Developer Guide. Select Symmetric and and so click Next. Recommended read: Symmetric vs Asymmetric Encryption Enter an allonym for this key. This is just an arbitrary human-friendly name you'll be using to refer to this key here in the AWS environment and in your JSCAPE MFT Server Amazon S3 trading partner object. You may also add a short clarification if you desire. Click Adjacent to keep. Next, select the IAM user who you want to administrate this central. In my case, I'm merely using my own user account. After that, select the IAM user who you desire to use this CMK in cryptographic operations. Over again, I'm just choosing my ain user account. Click Next to proceed. Lastly, click Finish to finalize the CMK creation process. You should and then come across your newly created customer principal key among your list of CMKs. Now that you accept your CMK ready, the next footstep is to assign that primal to an Amazon S3 bucket. Go to the AWS S3 service ... and then click the bucket whose data you want to encrypt with AWS KMS. Navigate to the Default encryption section and then click the text at the bottom. Unremarkably, that would be AES-256. When the Default encryption dialog box pops up, select the AWS-KMS option and then click the alias of the CMK you created earlier. In my instance, that would exist 'jcv-testkey'. Click Save to keep. The text at the bottom of the Default encryption section should at present display AWS-KMS instead of AES-256. That's all y'all demand to do on the AWS Management Panel. You lot may now proceed to your JSCAPE MFT Server instance and edit your Amazon S3 trading partner. In my case, the proper noun of my S3 trading partner is 'tp-s3'. Once you're inside your Amazon S3 trading partner parameters dialog, scroll down to the Authentication section. Make sure the Access Fundamental ID of this S3 trading partner is the access key ID of the username yous used in creating the CMK. Tick the Apply encryption check box and then select the region that matches the region displayed when you created your CMK. In my case, that would exist The states East (Ohio). Subsequently that, select the AWS-KMS option and aggrandize the adjacent driblet-down list. Click the allonym of the CMK you created earlier and and so click OK to apply the changes. That'southward all at that place is to information technology. Earlier nosotros end, let me just prove you what happens when yous upload a file to your AWS-KMS-protected Amazon S3 bucket from JSCAPE MFT Server. What I accept here is a trigger that uploads a file to my Amazon S3 bucket. Then, as y'all can encounter, the Partner setting is set to tp-s3, which is the proper name of my Amazon S3 trading partner object. The file this trigger is configured to upload is named file01.txt, and it'south going to exist uploaded to the folder named 'folder1' nether the S3 bucket named 'jscapejohn'. So, if I run this trigger... ... and check inside the S3 bucket folder named folder1 through the AWS Direction Console, I should see the newly uploaded file named file01.txt. If I click on that file and check its properties, I run into that it has indeed been encrypted with AWS-KMS encryption. That'south it. Now y'all know how to utilise AWS KMS to encrypt files uploaded to your S3 trading partner using JSCAPE MFT Server. Desire to attempt this out? Download the free, fully-functional Starter Edition ofJSCAPE MFT Servernow. Lookout man the video
Get started

Related content
How To Copy Information From Azure To AWS S3 | JSCAPE
How to Download Newly Added Files from an AWS S3 Folder
How To Schedule Automated File Uploads From Your Server To Box Cloud Storage
How To Employ Amazon S3 As The File Storage Organization of Your MFT Server
Amazon S3 vs Local Storage - Where Should Yous Shop Files Uploaded to Your File Transfer Server?
Topics: JSCAPE MFT Server, Managed File Transfer, Business Process Automation, Cloud Computing, Tutorials, Triggers
Source: https://www.jscape.com/blog/using-aws-kms-to-encrypt-files-you-upload-to-your-s3-trading-partner
0 Response to "Utilize Kms for File Upload to S3"
Post a Comment